Why Protocol Choice Matters
When you connect to a VPN (Virtual Private Network), the “protocol” is the set of instructions that determines how your data is routed between your device and the VPN server. It dictates the balance between speed, encryption strength, and stability.
For network administrators and privacy-conscious users, choosing the ‘default’ setting is no longer enough. To achieve specific goals—such as low-latency gaming, banking-grade security, or bypassing deep packet inspection (DPI)—you must select the right tool for the job.
1. WireGuard: The New King of Speed
Best For: Speed, Mobile Devices, and Modern Security.
WireGuard has revolutionized the VPN industry. Unlike older protocols with hundreds of thousands of lines of code, WireGuard is lean (under 4,000 lines), making it easier to audit and significantly faster.
-
Technical Specs: Uses state-of-the-art cryptography (ChaCha20 for encryption, Poly1305 for data authentication, Curve25519 for key exchange).
-
Pros:
-
Blazing Fast: Lower latency and faster throughput than OpenVPN.
-
Instant Connection: Handshakes happen in milliseconds.
-
Roaming: Handles network changes (switching from Wi-Fi to 4G) seamlessly.
-
-
Cons:
-
Privacy Concerns: Default configuration requires storing user IP addresses on the server (though premium VPNs have created workarounds like “Double NAT” to solve this).
-
Verdict: WireGuard is currently the Fastest and Most Popular for general consumers.
2. OpenVPN: The Gold Standard
Best For: Compatibility, Security, and Flexibility.
For nearly two decades, OpenVPN has been the industry standard. It is open-source and highly configurable.
-
Technical Specs: Uses the OpenSSL library and supports a vast array of encryption algorithms (AES-256-GCM is standard). It can run over UDP (faster) or TCP (reliable, bypasses firewalls).
-
Pros:
-
Battle-Tested: Audited thoroughly for security vulnerabilities.
-
Port Flexibility: Can be configured to run on Port 443 (HTTPS), making it harder to distinguish from regular web traffic.
-
-
Cons:
-
Bloated: Slower than WireGuard due to code complexity.
-
High Overhead: Requires more processing power.
-
Verdict: OpenVPN is the Most Common and Most Secure (due to its long history of audits).
3. IKEv2/IPsec: The Mobile Guardian
Best For: iOS users and Unstable Networks.
Internet Key Exchange version 2 (IKEv2) is often paired with IPsec for encryption. It is natively supported by iOS, macOS, and Windows.
-
The “MOBIKE” Feature: Its superpower is stability. If your connection drops (e.g., entering a tunnel or switching cell towers), IKEv2 re-establishes the connection immediately without the user noticing.
-
Pros: Very stable, native OS support (no app installation required).
-
Cons: Can be blocked easily by firewalls as it uses fixed UDP ports (500 and 4500).
4. The “Undetectables”: Protocols for Anti-Censorship
Best For: Bypassing the Great Firewall (GFW) and strict filtering.
Standard protocols like WireGuard and OpenVPN have distinct “fingerprints” that sophisticated firewalls can identify and block. To bypass this, we use obfuscation and proxy-based protocols.
A. V2Ray (VMess/VLESS) & Xray
V2Ray is a set of tools for building specific network proxies. It is highly effective in regions with heavy internet censorship (Iran, China, Russia).
-
How it works: It mimics legitimate web traffic. It can route traffic through a CDN (Content Delivery Network) or use WebSockets + TLS to look exactly like a user browsing a secure website.
-
Verdict: Currently the Most Undetectable method.
B. Shadowsocks
Originally designed to bypass the GFW in China. It is not a full VPN protocol but a secure split-proxy.
-
Features: Lightweight and creates a secure connection to a SOCKS5 proxy. It is very hard for Deep Packet Inspection (DPI) to identify as VPN traffic.
C. Obfsproxy (Obfuscated OpenVPN)
This wraps OpenVPN data packets in an obfuscation layer to remove the header information that identifies it as a VPN, making it look like random noise or regular HTTPS traffic.
5. Protocols to Avoid (The Graveyard)
-
PPTP (Point-to-Point Tunneling Protocol): Obsolete. It has serious security vulnerabilities and can be cracked in minutes by the NSA or hackers. Do not use.
-
L2TP/IPsec: Secure but slow due to “double encapsulation.” It is easily blocked by firewalls because it relies on fixed ports.
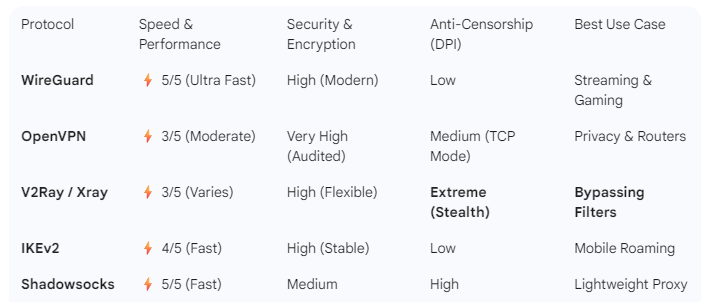
The “best” protocol depends entirely on your environment:
-
For maximum Speed: Choose WireGuard. It is the modern standard for 90% of users.
-
For maximum Security: Choose OpenVPN. It is the trusted veteran for banking and sensitive data.
-
For bypassing Filtering (Iran/China/Russia): Choose V2Ray (VLESS/VMess) or Shadowsocks. These are the only reliable options against Deep Packet Inspection.
By understanding these technical distinctions, you optimize not just your internet speed, but your digital sovereignty.