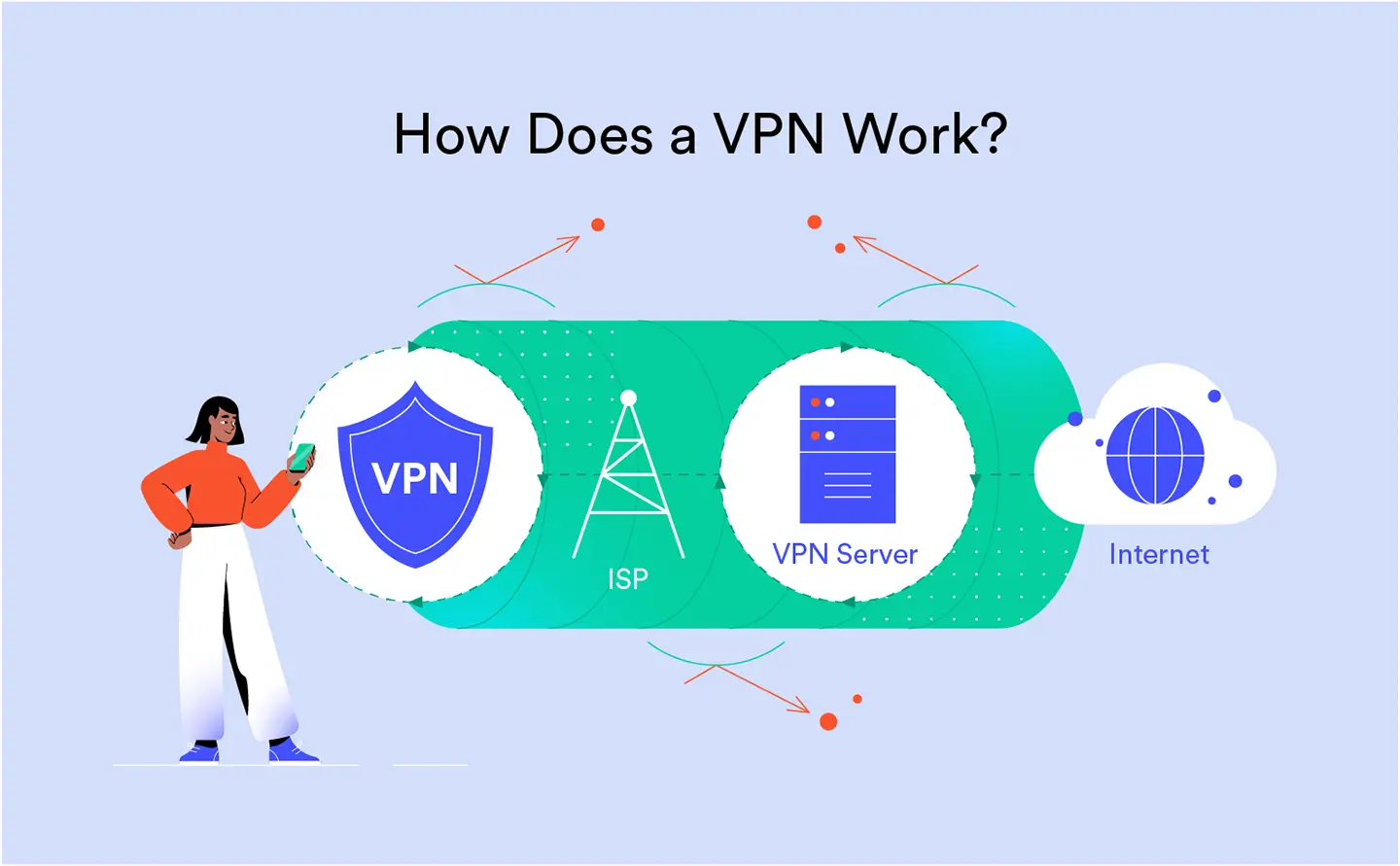
In today’s digital world, online privacy and internet freedom are more important than ever. A Virtual Private Network (VPN) is a powerful tool designed to protect your personal data and help you bypass strict internet censorship. By creating a secure, encrypted tunnel and hiding your real IP address, a VPN stops hackers, service providers, and government firewalls from tracking your online activity. Read this simple, easy-to-understand guide to discover exactly how VPN technology defeats geo-restrictions, keeps your connection safe, and gives you full access to a truly free and open internet.
Continue readingTop 3 Best V2Ray Clients for Stable Internet: V2RayNG, NPV Tunnel, and V2RayN
To enjoy a secure and fast internet connection using V2Ray, choosing the right client application is crucial for stability. This article provides a comprehensive review of the three best V2Ray apps available for different platforms. We recommend V2RayNG as the gold standard for Android devices, NPV Tunnel for a modern and fast experience on iOS, and V2RayN as the ultimate powerful tool for Windows PCs. Read on to discover which app is the most reliable choice for your daily browsing needs.
Continue readingV2Ray: The Ultimate Evolution in Modern Network Freedom
V2Ray is a powerful, multi-protocol framework designed to bypass the world’s most sophisticated internet censorship systems. Unlike standard VPNs like OpenVPN or WireGuard, V2Ray uses advanced obfuscation and TLS camouflaging to hide your traffic as regular web browsing. This makes it nearly invisible to Deep Packet Inspection (DPI) in highly restricted regions like China and Iran. By supporting versatile protocols such as VMess, VLESS, and Trojan, it offers unmatched flexibility and resilience against IP blocking. If you need a reliable solution for true digital freedom where traditional VPNs fail, V2Ray is the ultimate choice. Read our comprehensive guide to discover why V2Ray is the future of online privacy.
Continue readingThe Definitive Guide to VPN Protocols in 2026: Speed, Security, and Anti-Censorship
This comprehensive guide provides a technical analysis of the leading VPN protocols in 2026, including WireGuard, OpenVPN, IKEv2, and V2Ray. We dissect the critical trade-offs between encryption architecture, throughput speed, and network stability to identify the optimal solution for specific user needs. Special focus is placed on obfuscation techniques and “stealth” protocols designed to bypass Deep Packet Inspection (DPI) and strict internet censorship. Whether your priority is low-latency gaming, banking-grade security, or total undetectability against firewalls, this article equips you with the essential knowledge to choose the superior protocol for your digital privacy.
Continue readingWhy Do I Need a VPN? 5 Essential Reasons for Privacy and Freedom in 2026
In 2026, a VPN is an essential tool for digital survival, offering military-grade encryption and total IP anonymity. This article analyzes how a VPN protects you on public Wi-Fi, bypasses global geo-restrictions, and prevents ISP bandwidth throttling. Learn why securing your online footprint is the definitive step toward reclaiming your privacy and accessing a truly borderless internet.
Continue readingThe Great Disconnect: How Iran Systematically Killed the Internet in January 2026
The “Great Disconnect” of January 2026 marked a historic shift in Iran’s digital landscape, transitioning from standard filtering to a systematic infrastructure amputation. Through advanced behavioral DPI, IPv6 eradication, and protocol-specific jamming, the state effectively isolated 85 million users from the global network for twenty days. This technical deconstruction neutralized even the most resilient circumvention tools, creating an absolute “white-list” regime. The event serves as a grim blueprint for how state-level engineering can achieve total national isolation from the global internet.
Continue readingHow to Choose the Best VPN: 7 Key Features You Need to Know
To select the right VPN, prioritize seven essential features. Key requirements include strong AES-256 encryption and a strict no-logs policy for privacy. Ensure high speeds and a vast server network for accessing global content. Crucial additions are a Kill Switch for safety, user-friendly apps, and 24/7 support to guarantee secure, free internet browsing.
Continue readingV2Ray: Unpacking the Power of Speed, Security, and Privacy
While V2Ray is highly valued for its effectiveness in providing flexible and reliable network connections, its core design offers significant advantages in three critical areas for any discerning user: speed and performance, robust security, and deep digital privacy. V2Ray is the backbone of Project V, an advanced network framework developed to provide highly configurable, next-generation network connectivity.
Continue readingQuick Guide: Get Your V2ray Plan Instantly with Nowpayments Crypto
Pay for your V2ray plan securely using crypto via NOWPayments. The key is precise execution: Always match the exact network (e.g., USDT-BSC) to avoid permanent loss, and remember to add your exchange’s transfer fee to the required amount for instant activation. Send the calculated total and keep the payment window open until confirmed to receive your Subscription Link immediately.
Continue readingHow to surf safely on browser
Staying secure online is easy by following seven simple rules. Always update your browser and look for the HTTPS lock before entering data. Use unique, strong passwords with a Password Manager, and enable 2-Step Login (2FA). Be cautious of phishing scams, check download sources, and clear your cookies regularly to manage your privacy.
Continue reading